Security Aspects in Software Development
Table of Content
Content
The course provides insights into the security aspects of software developed in C and C++. This includes the ability to recognize and classify bugs, (efficiently) find bugs, exploit bugs, fix bugs, and prevent bugs in the first place. In the lecture part, we provide the theory behind these topics and we learn about state-of-the-art techniques and how they work. In the first part of the practical exercises, you have to find and exploit bugs in (vulnerable) code we provide (so-called hacklets). In the second part of the practical exercises, you write your own secure code and we will try to find and exploit bugs in your code (Hint: we shall not succeed if you want to pass the course).Material
The slides are available here after the end of each lecture.| Date | Topic | Additional Information |
|---|---|---|
| 04.10.2019 | Introduction + Low Level | Slides (Print) |
| 11.10.2019 | Memory Corruption I | Slides (Print) |
| 18.10.2019 | Memory Corruption II & Environment | Slides (Print) |
| 25.10.2019 | Finding Bugs I | Slides (Print) |
| 08.11.2019 | Exploits | Slides (Print) |
| 22.11.2019 | Finding Bugs II | Slides (Print) |
| 29.11.2019 | 12:00 Bakk@IAIK | |
| 06.12.2019 | Defensive Programming | Slides (Print) |
| 13.12.2019 | Countermeasures | Slides (Print) |
| Holidays | ||
| 17.01.2020 | Exam | |
| 24.01.2020 |
Older slides can be found here
Administrative Information
Communication
Newsgroup tu-graz.lv.sicherheitsaspekte E-mail sicherheitsaspekte@iaik.tugraz.atLecture Challenges (VO)
During the lecture, we will present small "Lecture Challenges" as a bonus. These challenges are optional, but solving them results in bonus points for the VO exam.The Challenges
The aim of the challenges is to dig deeper into a certain topic of the respective lecture. Thus, it is advisable to try to complete the challenge soon after the lecture. The description of the challenges can always be found in the lecture slides as well as in https://sasd.is.attacking.systems.Submission
All challenges have to be submitted to https://sasd.is.attacking.systems, the SASD CTF platform.Rules
- Challenges have to be solved on your own
- All challenges have to be submitted to https://sasd.is.attacking.systems, only submitted challenges count
- The bonus points are only valid for the first two exam dates
- To get the bonus points, you have to write your username on the exam sheet
- You cannot get positive with bonus points, i.e., bonus points only count if you are already positive
Exam (VO)
Exams are done in writing. The dates for the exams are set in TUGonline; please register there. Exams consist of both theoretic questions and practical questions. Theoretic questions are basically the theoretic parts of the slides and possibly additional content presented in the lecture which are not part of the slides. Practical questions are, in principle, similar to the tasks given in the lecture challenges as well as in the practicals. However, the complexity of the questions is scaled to make them adequate for the time available during an exam. All questions of the exam are in English. Answers can be given either in English or in German, at the student's discretion. No lecture notes, or any other materials are allowed during an exam. All materials required to solve the practical questions are provided at the exam. The provided material includes an ASCII table, a C function reference for required functions, and a table containing the required syscall parameters.Sample Exams
We also provide old exams to help you prepare for the exam:Administrative Information - Practicals (KU)
Timetable
| Date | Topic | Additional Information |
|---|---|---|
| 02.10.2019 | Introduction + Assignment 0 - Warmup | i12, Slides-00, Slides-01 |
| 09.10.2019 | Hands-on Tutorial | Seminar room, Material |
| 09.10.2019 | LosFuzzys Beginner's Tutorial | Seminar room, optional, in the evening |
| 16.10.2019 | Assignment 1 - Hacklets + Tutorium ROP I | i12, Slides |
| 18.10.2019, 23.59 | Deadline Warmup | |
| 23.10.2019 | Tutorium ROP II | i12, Slides |
| 30.10.2019 | LosFuzzys | i12, optional |
| 06.11.2019 | Question Hour Hacklets | i12, then moving to small seminar room IFEG052 |
| 13.11.2019 | Question Hour Hacklets | Seminar room |
| 15.11.2019, 23.59 | Deadline Hacklets | |
| 20.11.2019 | Assignment 2 - Defensive Programming | i12, Material, Slides |
| 22.11.2019, 23.59 | Deadline Hacklets 2nd Chance | |
| 27.11.2019 | Tutorium Defensive I | i12, Material |
| 04.12.2019 | Tutorium Defensive II | i12, Material, Slides |
| 11.12.2019 | Question Hour Defensive Programming | Seminar room |
| Holidays | ||
| 08.01.2020 | Question Hour Defensive Programming | Seminar room |
| Deadline Defensive Programming | ||
| 17.01.2020, 23.59 | Deadline Defensive Programming 2nd Chance | |
| 22+23.01.2020 | Oral Exams | Seminar room, mandatory |
Grading
The practicals are divided into three parts:
assignment0: Warmupassignment1: Hackletsassignment2: Defensive programming
-
Points for each assignment
-
Bonus points count only if you have achieved 50% of the assignments points
-
-
Oral exam performance
(percentage(assignment1) + percentage(assignment2))/2 * percentage(OralExam)
Marks
| Percentage | Grade |
|---|---|
| > 90% | Sehr gut (1) |
| 78.5% - 90% | Gut (2) |
| 67.5% - 78.49% | Befriedigend (3) |
| 50% - 67.49% | Genügend (4) |
| < 50% | Nicht genügend (5) |
Oral exam
After the deadline of all assignments, there will be an oral exam. The oral exam is mandatory. You will have the option to select one of the multiple time slots where you need to be able to answer questions to each assignment and task that you fulfilled.
However, insufficient answers will yield to point deduction that can even yield to a negative grade. We will provide more information on what you need to know for the oral exam for each assignment individually.
Plagiarism
We encourage discussions with other students and really appreciate that. However, we do not tolerate any plagiarism at all. We will check all submissions for plagiarism. All affected students will receive 0 points and a Ungültig/Täuschung with all its consequences.
Thus, do not give away your source code to other students. You are responsible for protecting your source code from unintended access of others. In the end, we do not want you to copy code and solutions. We want you to learn and understand the topics for yourself!
Second chance
If you fail one assignment but you pass the other, there is the option to take a second chance. The second chance mode means that you have the possibility to get a positive grade by an extended deadline and an individual, extended oral exam:- Only for one assignment
- Extended deadline
- Extended oral exam
- Points above 50% are divided by two for this assignment
Practicals - Framework
Upstream Repository
All assignments are pushed to the following upstream repository: https://extgit.iaik.tugraz.at/sase/practicals/2019/exercise2019-upstream.git. Merge this upstream repository into your local repository to receive the assignments and optional patches or fixes, as follows:git remote add upstream https://extgit.iaik.tugraz.at/sase/practicals/2019/exercise2019-upstream.git
git pull upstream master
Your Repository
As soon as the deadline for the course registration closes, you are given access to a git repository in our teaching git where you have to push your submission. This will happen around 14.10.2019. Until then, please use an empty local repository by following these instructions:
mkdir sasd2019
cd sasd2019
git init
git remote add upstream https://extgit.iaik.tugraz.at/sase/practicals/2019/exercise2019-upstream.git
git pull upstream master
Final submission / Tags
Your final submission must be tagged correctly with a
git tag. The tag label starts with the assignment, followed by a dash and a number.
As an example, assignment1-1 is the label for the first assignment. As you are not able to delete tags, you can always update your final submission by increasing the appended number, e.g. assignment1-15. In the end, the tag with the highest number before the deadline counts.
Test system
Your submissions will be tested automatically by our test system. Thus, you need to respect and meet file naming constraints of the individual assignments. Otherwise, the tests will all fail and you will receive 0 points for the assignment.
Soon, you will receive binary feedback for each task group that you have submitted. You will know if the project compiles and if your implemented functions will behave correctly or if your submitted solution is correct. The test system will use the reference image for its evaluation.
Reference image
We provide you a Docker reference image. The reference image is based on Ubuntu and contains pre-installed tools and compilers that help you throughout the assignments. The Docker image can be used via the docker.sh script located in the upstream repository. To fetch it, execute
git pull upstream master
To get the latest Docker image, execute ./docker.sh update
To run Docker in the current directory, execute ./docker.sh run
To run Docker in a different directory named <path>, execute ./docker.sh run <path>
If you run this script inside a hacklet directory, it automatically executes the execute-permission.sh script which runs your exploit with correct permissions.
Practicals - Assignments
Assignment 0 - Warmup
In this assignment, you shall solve an introductory hacklet to get started. While this assignment is mandatory, you do not get any points. Instead, by solving it you show your intent to actually do this course. If you do not solve it, you won't get a grade. Submission tag:assignment0
Deadline: 18.10.2019, 23.59
Assignment 1 - Hacklets
In this exercise you take the role of a security consultant, who has been asked to audit multiple small C and C++ applications, let them be called ”hacklets” for the remainder of this document, for potential security issues. After a series of strange incidents, bad news coverage, and an increasing number of bug reports by angry users claiming loss of data and disclosure of private information due to security problems in the hacklets, you have been hired to audit the code. Note that your fictional employer in this scenario currently considers information security as a nice-to-have-butnot-mission-critical-if-missing feature.
Submission tag: assignment1
Deadline: 15.11.2019, 23.59
Organizational
-
You can achieve 22 regular points, which equals 100% for assignment 1.
-
For a positive grade you need to achieve at least 11 points in total AND at least one point in each regular category (except bonus category).
-
You can achieve 3 additional bonus points by solving bonus challenges.
- The bonus points only count if you are positive using regular points only.
Hacklets: Oral Exam Part 1
-
You have to defend your points during the oral exam at the end of the semester, which is mandatory.
-
During the oral exam, you have to explain for the solved hacklets:
-
Problem statement: Where is the vulnerability? What is the problem? Why is this dangerous? …
-
Exploit: How does your exploit work? Which security mechanisms did you bypass and how? …
-
Mitigation (only if the source code is available, i.e. no reverse-engineering hacklets): How would you fix the vulnerability in the source code? Which other defenses would work/would not work and why? …
Flag format
All hacklets except some hacklets, as indicated below, use the following flag format
SASD{[A-Za-z0-9_!]{26}}, e.g. SASD{TH1S_IS_A_local_TEST_FL4G!}.
Test
… your exploit on the provided VM by running
./exploit inside the hacklet directory. On success, it shall print the above demo flag to stdout. In addition, the exploit has to write the flag to a file named solution.txt. We will test your exploit with different flags. You will only get points for a hacklet if the flag is recognized.
Fair Play
-
Do not plagiarize. If you do so, you will get zero points and fail the course.
-
Do not manipulate the hacklets inside your exploit scripts, e.g. disabling ASLR, preloading, etc. where it is not explicitly allowed. Especially, your exploit scripts are not allowed to use root privileges. We expect you to solve the hacklets in the intended way. In case of doubt, ask in the newsgroup.
-
Any attempt to attack our server infrastructure will disqualify you from the course
Hacklets
00_strings
- Cryptomaster(1pt):
- The crazy Cryptomaster hid some hidden secret in his code where he claims that you never crack his code! Maybe some hashing skills might help you to defeat him.
- Terminator(1pt):
- Show me your terminator skills!
01_environment
- cmacro(1pt):
- This is a really nice macro which every programmer should use. Maybe you brick the environment to extract the flag.
- fast_math(1pt):
- Race to the condition and prove that you are good at fast math.
- pluginsystem(1pt):
- Can you show us the problem in the plugin system. Hint: You can also write your own plugins ;)
- preload_me(1pt):
- You know what to do!
02_buffer
- combined (2pt):
- Use a format string vulnerability and a stack-based buffer overflow in order to bypass stack protection.
- echo_service (1pt):
- Can you guess to delicious stack cookies in a smarter way? Forket it!
- my_first_rop_chain(1pt):
- In this challenge no pwntools ROP tools are allowed! Just ROP it by hand and use the gathered knowledge to rock your lecture exam ;)
- random_pin_generator(1pt):
- I am really bad at remembering PIN codes, can you find another way to get to my money?
03_integer
- callcenter(1pt):
- There are callcenter employees complaining about some crazy mathematical computations. Can you also trigger some of them?
- card_game(1pt):
- Do you like to play cards? Show how to win in this game ;)
- nice_sequences(1pt):
- Who of you does not like integer sequences. Can you show a tremendous flaw in this program?
- pgminverter(2pt):
- This hacklet parses simple images in PGM format and applies the Number Theoretic Transform with user-provided filter-coefficients on 8×8 block in the image. Can you find a problem within the code?
- rust(1pt):
- Rust is safe of memory corruption issues and overflow problems, right?
04_heap
- calculator(1pt):
- A friend of mine wrote a nice program which contained a nice debug feature do you know what that is?
- heap_overflow(2pt):
- They told me that there should be a heap overflow inside this binary. Can you show me that?
05_format-strings
- guess_a_number(1pt):
- Are you good at number guessing? Do you even need to guess?#
- reveal_the_secret(1pt):
- Eddie Snowden hid a secret information from the NSA in the binary. Could you reveal it exploiting a format string vulnerability?
06_bonus
- 1pt angr_management(1pt):
- You should really use some symbolic execution to manage your angr my friend!!
- turing_completeness(2pt):
- Turing completeness nowadays is nearly everyday. Did you know that x86-mov is Turing-complete? :) Have fun with reversing this hacklet :)
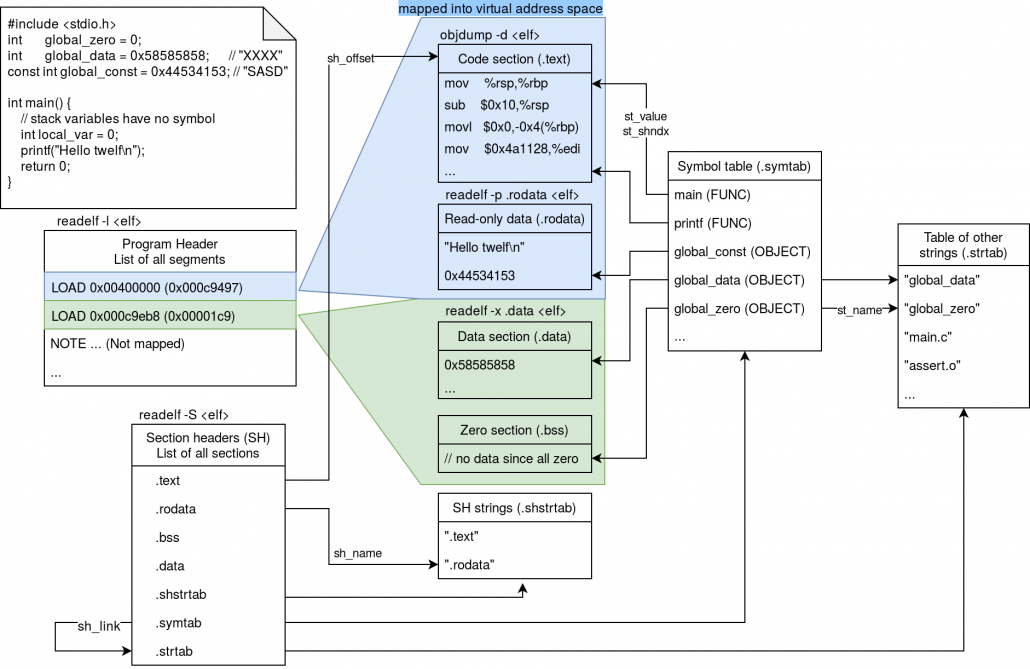
Assignment 2 - Defensive Programming
Iin this exercise you shall implement a secure ELF parsing library called libtwelf. Submission tag:assignment2
Deadline: Organizational
- You can achieve 100 regular points, which equals 100% for assignment 2.
- You can earn 12 additional bonus points (if you are already positive):
- 5 bonus points for having high code coverage in your test cases
- 4 bonus points if you implement ELF symbol handling functions
- 3 bonus points if you store the (modified) string tables (
.shstrtaband.strtab) in their minimal form
- You lose -3 points for each of the following issues (even if not exploitable)
- Program crash
- Memory corruption, memory leak, use after free, use of uninitialized memory (or other stuff reported by valgrind, address sanitizer & co)
- Format string vulnerability, integer overflow
- You lose -3 points for each of the following issues
- Undefined behavior, e.g.
(void*)x + 1 - Non-portable, hidden assumptions, e.g.
sizeof(int) == 4 - Hard-to-read or dangerous code, e.g.
#define FUNC(x) x=x*x - Use of global variables. They are not needed for this library.
- Compiler warnings, e.g.
printf("%u", (long long int)x)
- Undefined behavior, e.g.
- Plagiarism is not tolerated
- You are not allowed to copy code snippets (neither from the internet nor from other colleagues)
- We will do plagiarism tests. Affected students will receive 0 points and get an "Ungültig/Täuschungsversuch"
Defensive: Oral Exam Part 2
-
You have to defend your points during the oral exam at the end of the semester, which is mandatory.
-
During the oral exam, you have to explain:
-
Source code: How does your implementation work? Why did you implement it in this particular way? ...
-
-
-
Issues: What is the problem? What can/cannot happen? Which mitigation technique would prevent exploitation? Explain defensive programming principles ...
-
-
-
Mitigation: Fix smaller issues in the source code
-
Tasks
The libtwelf provides different functions which you shall implement. The detailed specification for each function can be found inlibtwelf_write. In order to get full points for e.g. libtwelf_renameSection, the implementation must rename the section in your internal data structures as well as in the final file written with libtwelf_write.
| ID | Function name | Points | Dependencies |
|---|---|---|---|
| A | libtwelf_open/close |
20 | |
| B | libtwelf_write |
11 | A |
| C | libtwelf_getAssociatedSegment |
5 | A |
| D | libtwelf_getSectionData |
5 | A |
| E | libtwelf_renameSection |
9 (+2 bonus for minimal .shstrtab) | A,B |
| F | libtwelf_getSegmentData |
5 | A |
| G | libtwelf_setSegmentData |
9 | A,B |
| H | libtwelf_setSectionData |
9 | A,B |
| I | libtwelf_stripSymbols |
9 | A,B |
| J | libtwelf_removeAllSections |
9 | A,B |
| K | libtwelf_addLoadSegment |
9 | A,B |
| L | libtwelf_resolveSymbol |
2 bonus | A |
| M | libtwelf_addSymbol |
2 bonus (+1 bonus for minimal .strtab) | A,B |
Bonus: Code Coverage
For getting coverage bonus points, write your own exhaustive test cases. Branch coverage can be tested withmake gcov
| Overall branch coverage | Bonus points |
|---|---|
| 75% <= cov < 80% | 1 |
| 80% <= cov < 85% | 2 |
| 85% <= cov < 90% | 3 |
| 90% <= cov < 95% | 4 |
| 95% <= cov | 5 |
Resources
objdumpreadelfman elf- Wikipedia with nice overview graphics
- ELF Segments and Sections